How to Locate Aggressors and Nefarious People Online
How do you find out who anonymously posts information about you, your company, or your country online? We set up a fake company, imaginary CEO, social media, and fictitious backers to trap anonymous perpetrators posing as our clients’ Ministry of Finance. This is how we did it.
Our client, a country, had a problem with someone claiming to be a representative of their Ministry of Finance who was offering financial incentives for startups willing to relocate to their country. Of course there was a “small administrative fee” due in advance for their generosity. Clearly this negatively affected the country’s online reputation so we sprang into action!
In our case, we led the perpetrators into thinking we were interested parties located in yet another foreign country, we helped locate the thieves, and turned the information over to our client.
The problem was then magically solved. We like to think black stealth helicopters led by Tom Cruz were involved at some point.
How we found the bad guys
The bad guys we were trying to identify used a real Hotmail address, so we had somewhere to start. Still, Hotmail addresses use common servers that are usually not near where the person using the services is located.
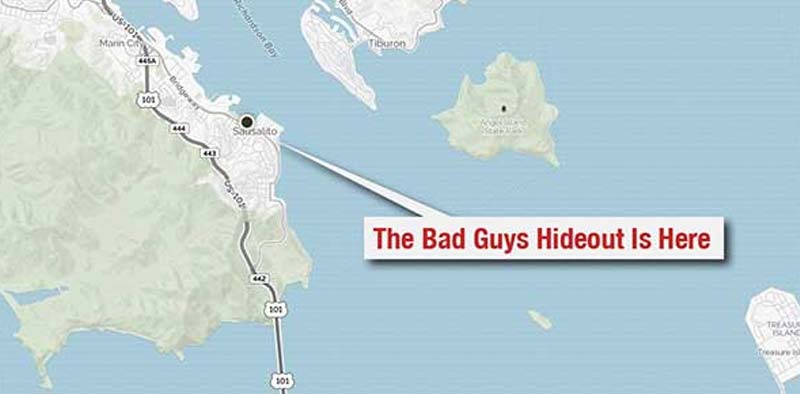
No matter what information you have to start with the key is the IP address – the unique numerical address that identifies where someone is accessing the internet from. An IP address will often tell you to a city level where an anonymous person is operating from – while not always perfectly reliable, sometimes it will tell you to within a few feet.
For example: the IP address on the map on this page shows my exact location outside the coffee shop at which I wrote this article in Sausalito, California.
As mentioned above, Hotmail, Gmail and other public email systems don’t reveal the true IP of someone. To do that you need the perpetrator to visit a website. But getting an anonymous person to voluntarily go to a website to locate their IP address and then send it to you probably won’t happen. So you have to get them to do it without knowing they’re doing it.
Find who the owner of an email address is using reverse email lookup
Have an email address but don’t know who they are? If you only have the e-mail address of a person but not their identity it may be possible to perform a reverse email lookup.
We sometimes use Spokeo.com’s reverse email identification tool. It’s simple, just input the email address and Spokeo will do the work of finding it in various online databases like social media, domain registration documents and more. But that didn’t work for our bad guys because they were operating in a foreign country using a one-time use email address, Hotmail in this case. They hadn’t used it for anything else so we had no additional clues at that point.
How to get an IP address even if the email is unlisted
If you have the email address of a person but cannot find information on it using a tool like Spokeo simply send them an email using a tool called ReadNotify. When you send an email using this service it will track whoever opens the email and provide quite a bit of information about them including their approximate geography, IP address and more. This is one of the methods we used.
Honeytrap – Building a juicy target
We developed a false company name, a logo, an imaginary CEO with a complete biography (even imaginary kids). We even created the appearance of false financial backers for our “established” business with blog articles, bio pages and more, in order to get the perpetrators to believe we were a real mark.
We made sure the back-story was believable to the point of having authors write glowing stories about our fake company. Because the fake company was located in a foreign country we translated everything into the local language. We even made the social media profiles active. To do that we used HootSuite to setup timed Tweets. That way we could write and translate them all at once, load them in bulk into a spreadsheet and set them for later posting.
Inviting bad people over for tea
If you cannot get perpetrators to respond to a rigged email that identifies their location, you may be able to get them to visit a honeytrap website that will reveal their IP address, and that can be hard. This can sometimes be done by adding a comment to negative post online.
When someone flames you or your brand online you may be able to comment on it and add a link to an “apology” or other lure that exists in another place online, your honeytrap website, but others might visit too. If you can, contact the offending poster directly via direct message (if the site they commented on has that) or if they provided a special email, use that.
The important thing is to get them and them alone to come to a page within the site. Once they do you’ll probably know where they are. But how do you identify them?
Building an electronic mousetrap to catch bad guys

Strawmen
To trap our thieves we setup a website for the fake company located in yet another foreign country, we setup Twitter accounts, Facebook and LinkedIn too.
A cursory look by the bad guys revealed a CEO, a technology company startup and apparent financial backers. It all looked real and was created in both English and the local language.
How You Can Find Anonymous People Online
While our methods are reasonably sophisticated, you can set up your own honeytrap blog using a hosting service like GoDaddy and opting for a WordPress installation. But there are a lot of other vendors out there, like HostGator and Squarespace (not WordPress, untested, but very easy).
This way the blog becomes a trap for the anonymous troll/attacker/blogger/scumbag. Anyone who comes to the blog will have to do it from an IP address, and unless they are obfuscating (hiding) their IP address, you may know who it is based on location alone (Hey, it’s that guy I flipped off in San Rafael!).
You can track IP addresses with software you place on your site like StatCounter which logs the IP of visitors. Use Google Analytics. Here is an article that tells you how to get an IP address using it (we’ve not used this method).
You can either make the whole site invisible to search engines, or just a page. I’ll talk about both.
Making your honeytrap site invisible
NoIndex tags will keep search engines from crawling a site, but sitemaps are important too. A website sitemap tells search engines where all your pages are if they were created dynamically, like what WordPress does. Make sure your site does not automatically add pages to a sitemap if you can because you don’t want any bots crawling the site, and a sitemap leads bots like Google right to all of your pages. The reason you don’t want a sitemap (like an XML sitemap file) is because within the site you will build a page that has no links to it from anywhere else on the site. This page should exist in a vacuum. Only one person should ever visit this page other than you – your target.
Making a single page in your site invisible
You could also make only a single hidden page invisible. On that page would be the StatCounter code. A good way to do this is to build the page with good old-fashioned HTML instead of using WordPress. If you have the technical chops to do it, we recommend this method to be sure it isn’t linked to anything else. This way you have a page with your “apology” or whatever content you use to lure the anonymous user to the page.
How we filtered out the wrong users
In our example with the Ministry of Finance, we made sure our site looked real, but invisibly it turned search engine robots away. That narrowed down the users who came to the site to a handful we had lured with online comments and responses to emails. While this was helpful, it wasn’t the thing that really identified them – that ended up being the email tracking mentioned above. The website, while it could have identified the perpetrators, was there to verify us as likely dupes for their internet thievery. But the IP addresses on the site matched those from the email, so we had two data points to compare.
In the end we found them
In the end, we identified their email, IP address, location, language, mailing information, and more. We turned the information over to the government that hired us to help turn around their online reputation. They did what governments do and the problem went away.
We removed much of the work we did when the project was over. This effort was an example of international online reputation management and included creative thought, content strategy, web development, search engine optimization, email tracking, social media, foreign language translation, and some luck. All working together to make the world a better place.
Read This: Changing Googles Knowledge Graph
Finding Anonymous People Online FAQs
How can you find anonymous people online?
You can find anonymous people online by setting up a honeytrap website. You can track IP addresses with software you place on your site like StatCounter which logs the IP of visitors.
How can an IP address be used to identify a person?
An IP address will often tell you to a city level where an anonymous person is operating from – while not always perfectly reliable, sometimes it will tell you to within a few feet.
How do you find a person’s identity based on their e-mail address?
A reverse e-mail lookup can help you identify the owner of an e-mail address. Spokeo.com has a good tool for this.
How do you find a person’s IP address if the email is unlisted?
You can send an email using a tool like ReadNotify to track whoever opens the email. You can collect information such as their approximate geography, IP address, and more.
Tags: Business Reputation Repair.