Masking Identity on the Internet – Protecting Identity Online.
Most people around the world wore masks due to the pandemic. But can you wear a mask online? Yes, you can.
Online identity management is a subset of online reputation management in that it deals with the management of who a person appears to be online.
One example of online identity management is the use of different personas for various online interactions in an attempt to mask personal identity exposure.
Another is the use of someone’s true persona online, but in a carefully managed way using the following strategies:
You can use dual online identities to mask online movements
In the post-privacy age, the management of one’s identity online has become more important than ever.
Disclosure of one’s true identity can open a person up to documented criticism that can never be expunged. Using one’s true identity is necessary in many instances, LinkedIn being one example.
But in a time when opinions are twisted, misrepresented, and can, in some cases, become viral reputation landslides, it is often best to manage a separate identity for online discussion.
Pseudonyms: Protection from search engines
It’s a brutal world out there. Many people make the mistake of exposing their true identity online when voicing an unpopular position. As a reward, they are often lambasted, abused, or accused of many unrelated things.
The permanence of search results means that it is now common for individuals to end up with ruined reputations by simply exercising their right to an opinion.
It has almost become necessary to cultivate either an alternate persona online (a pseudonym) or to mask oneself behind a wall of anonymity if one is to hold contrarian views online today.
“Opinion is really the lowest form of human knowledge. It requires no accountability, no understanding. The highest form of knowledge… is empathy, for it requires us to suspend our egos and live in another’s world. It requires profound purpose larger than the self kind of understanding.” – Bill Bullard
The problem with exposing oneself online is that one’s opinion may be the object of other people’s opinions, a risk in the Wild West of the internet. Pseudonyms are a tool to mitigate that risk.
Be like Demosthenes and Locke
The book Enders Game discusses the online conversations between pseudonyms used by a brother and sister with apparently contrary viewpoints. Their online identities were Demosthenes and Locke. Set in a post-privacy future, they engage in conversations that would have been fatally unpopular.
IP addresses are tracked – remember that
When you comment online, change a Wikipedia page, or engage in social media, your IP address is tracked and recorded by someone.
If you want to stay anonymous, change your IP address. This can often be done by restarting your router, but services like TOR and proxy services can help dilute your tracks.
How revenue models online fuel reputation destruction
Today, reputations can be destroyed by one strong website attacking the opinions of an individual.
An article by a blogger or journalist intended to get the publication a few more hits, and therefore advertising revenue, can permanently destroy the reputation of its subject.
It has been our experience that the journalist either blithely ignores those she has hurt or is oblivious to the lives affected. Years after the journalist has moved to another career, those people her opinions affected are often still suffering.
But it isn’t all the journalist’s fault. On their own, the damage wouldn’t be so widespread. But search engines magnify their opinions a thousandfold to the point where to be safe, pseudonyms and anonymity are becoming necessary aspects of modern life.
Managing true identity by sculpting online profiles
Why let a corporation like Google decide your online fate?
Thankfully, it isn’t necessary to continually hide behind a wall of anonymity because a person’s true identity online can also be managed. The dangers of espousing unpopular opinions online can be mitigated by relegating more combustible comments to a pseudonym, while containing mainstream content to one’s real-world identity.
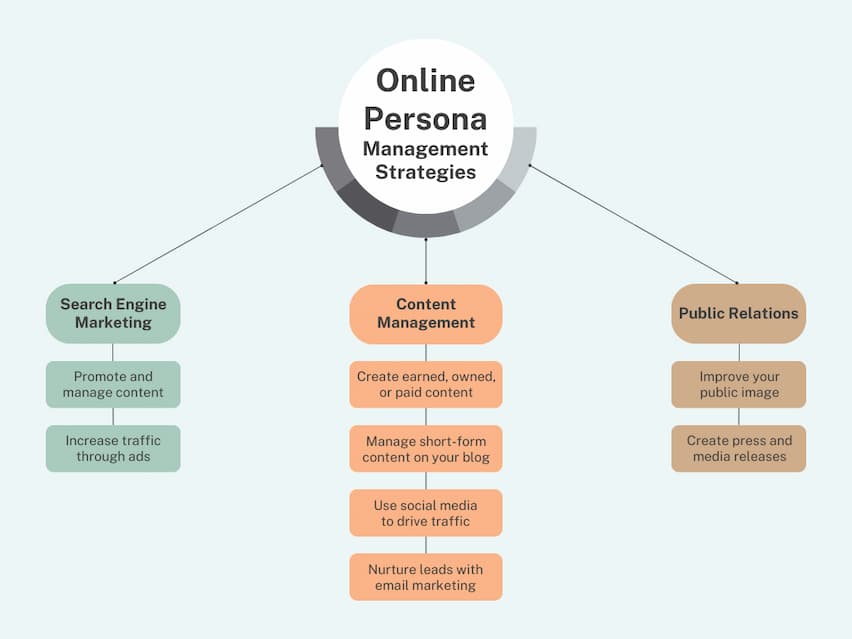
You can effectively manage your online identity through a combination of:
- Search engine marketing
- Content management
- Public relations outreach
By identifying controlled websites and optimizing the content on those sites, developing strong backlinks to pages on those sites, and keeping abreast of search engine algorithms, the most often seen search results reflecting online identity can be burnished.
Developing a personal mythology online
News sites, blogs, social media, forums, personal websites, video, and online imagery all contribute to the development of a personal mythology. A somewhat controllable network of pertinent online content designed to be consumed by search engine users can be grown.
Blogging, contributing to others’ blogs, a carefully messaged LinkedIn profile, and managing public information available on Facebook are all actions that can be taken to take back at least some control.
The objective of online identity management
The objective of online identity management is to be free to speak one’s mind online while both protecting and promoting one’s personal brand online. One of the most effective ways of doing this is to develop one or more pseudonyms used to interact online that do not overlap with a carefully cultivated public image.
Whether it be to protect an online reputation from detractors or to improve a damaged or weak online reputation, online identity management has become key in society today, especially for children and teens.
Online Identity Management FAQs
What is online identity management?
Online identity management is a subset of online reputation management in that it deals with the management of who a person appears to be online. It often works as part of a branding or reputation management campaign to improve the quality and accuracy of the information that comprises your online identity.
What is a personal mythology?
A personal mythology is a somewhat controllable network of pertinent online content designed to be consumed by search engine users. News sites, blogs, social media, forums, personal websites, videos, and online imagery all contribute to the development of a personal mythology.
How do I effectively manage my online identity?
A combination of search engine marketing, content management, and public relations outreach is useful for managing online identity effectively.
About the author
Kent Campbell is the chief strategist for Reputation X, an award-winning online reputation management agency based in California. Kent has over 15 years of experience with online reputation management, Wikipedia editing, review management, and strategy. Kent has helped celebrities, leaders, executives, and marketing professionals improve the way they are seen online. Kent writes about reputation, SEO, Wikipedia, and PR-related topics, and is an expert witness for reputation-related legal matters.
–
Tags: Online Reputation Management Services, Personal Branding.