How to Identify Someone Who Is Attacking You Online
Tracking down who is defaming you online isn’t always easy, but some tips and tricks can help. The key is using tools and strategies to gather identifying information about the anonymous poster. Finding their email and IP address is a good start.
Highlights:
- It has become easy for people to anonymously post false and damaging things about you or your company online.
- You can find out who defamed you online—even if they post anonymously.
- There are tools and tactics available to uncover information identifying the defaming person.
Who might be creating negative content about you online?
It’s an altogether too common occurrence. You see something untrue and damaging about you or your company that someone posted online. Anonymously.
If you instantly want to know who the person is that just defamed you online, you’re not alone. Good reputations are important and take time to build, and no one likes having mud slung at them unfairly.
It has become very easy for people to anonymously post negative, reputation-damaging content online, but it’s also possible to track these trash talkers if you know what you’re doing.
If you want to find who is defaming you online, keep reading.
Places to look for defaming comments about you, your company, etc…
There are many places online people can say things about you.
- Online message boards (i.e. Yahoo Finance Board)
- New URLs (YourCompanySucks.com for example)
- Emails to employees, clients, and competitors
- Wikipedia articles
These are just a few of the avenues where defaming comments about you or your company can show up, and these comments can be (and often will be) made using a fake and anonymous email address or screen name.
How to track negative information online
Even if a defamer is deceptively hiding behind an anonymous email or screen name, there are still ways to track them down and put an end to their nonsense.
The first thing you want to do is confirm who the email address belongs to that is behind the defaming comments. One way to do this is to use an online tool called Spokeo Reverse Email Lookup.
Once registered for this service, Spokeo will dive deep into the web and search everything from blogs to social networking sites to photo-sharing websites and beyond — all to confirm if the email address is active.
Sometimes the person posting defaming comments uses an old email address or has a pseudo address they use for multiple accounts. If they are using this kind of email address that isn’t fully anonymous, a simple Spokeo Report (if you pay the $1.95 fee) could reveal your perpetrator and end your search.
Even without the paid level, a tool like Spokeo will reveal whether or not the email address associated with the defamatory comments is an active email address that is associated with a real person. However, it will not tell you one of the things you need to know. That’s the IP address.
What is an IP address?
An IP address is a unique identifier for an electronic communication device that uses the internet or a local network. IP stands for “Internet Protocol,” which is the set of rules governing the data that is sent from these devices.
IP addresses at a glance:
- Each host on a TCP/IP network is uniquely identified at the IP layer with an address
- An Internet Protocol (IP) address specifies the location of a host or client on the internet, or a best guess
- The IP address is also known as Protocol address
- The IPv4 address is 32 bits long
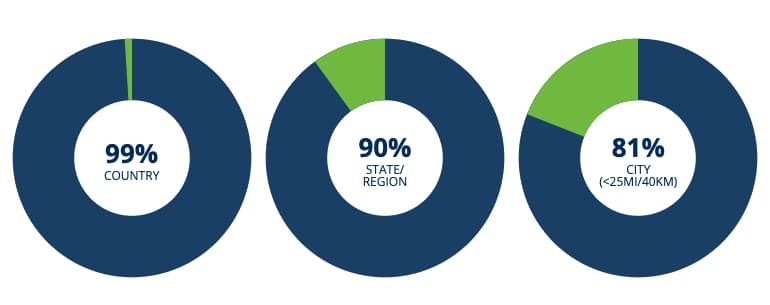
An IP address is part of a device fingerprint that can help you catch your trash talker. It can reveal a device’s geographical location within a certain range. It can also reveal device information such as the internet provider being used. With an IP address, you can pinpoint a location that is within 25 miles from the defaming device with around 81% accuracy.
What is a device fingerprint?
A device fingerprint is a way to identify a device or browser by collecting unique information about its configuration. You can sometimes create a profile of the person defaming you by using specific data points about their device and usage.
These data points include:
- IP address
- Browser plugins installed
- Time zone
- Installed fonts
- Timestamp
- Flash data from Flash plugin
- HTTP request headers
- Silverlight data
- User-agent string
- Mime-types
Device fingerprint trackers are pieces of code that collect and report all these various pieces of information and put them together to identify individuals on various websites or web pages. This unique fingerprint allows for more advanced tracking than mere cookies could ever provide. At this point, you may not know your hater’s name, but you know all about their defaming device.
How to find someone’s IP address
There are numerous ways you can track down an IP address, but it isn’t always easy and sometimes it can require a subpoena. For instance, if somebody changes your Wikipedia page anonymously and defames you or your company, access to the IP address will be contingent on a few things.
Wikipedia tracking
If the perpetrator logged into Wikipedia but used a fake account, their IP address will be viewable by Wikipedia and only obtainable to you by a subpoena. However, if they edited your Wikipedia page but didn’t log in, their edit will be anonymous but their IP address will be made public.
If you’re on the receiving end of a defamatory statement that isn’t on Wikipedia, there are also other ways to find your target’s IP address.
Snoop via email
If you have the person’s email address, but you need more information than the type provided by a service like Spokeo, you can send the person an email using a tool called ReadNotify.
When you send an email using ReadNotify, the service will track whoever opens the email and provide you with a bevy of information, including the IP address.
Once your email is opened, ReadNotify will automatically and discretely send you back a snapshot of:
- The recipient’s IP address
- The date and time the message was opened
- The location of the recipient (per their ISP city /town)
- A map of the location
- The apparent email address that opened it (if available)
- Referrer details (i.e., if accessed via webmail, etc.)
- URL clicks
- How long the email was read for
- How many times your email was opened
- If your email was forwarded to or opened on a different computer
Remember, you don’t have to have the person read the whole email or click on a link; you just need them to open the email – that’s the key. You want to hit them with a subject line that raises enough curiosity that they can’t resist but to open it.
Get creative and deliver a subject line that will entice a high open rate. Maybe try something like, “I know who you are,” or “I got you now…” Nearly half of email recipients decide to open an email based on the subject line. These types of subject lines are similar to clickbait.
Honeytrap websites
If you put a link to a “honeytrap” website in your ReadNotify email or attach a document to the email, and the recipient clicks on the link or opens the attachment, you can get even more useful information about them and their location.
A honeytrap website is a site used to tempt and lure a target by appearing to have something the target wants. The honeytrap’s endgame is to find out the target’s identity or identifying information. Once the target lands on the site, all sorts of information about them becomes instantly available – the target has now exposed their identity.
If you can’t get your defamer to engage with a rigged email, you can try to get the link to your honeytrap in front of them another way.
Use comments to locate someone
You could put the link in a comment you write in the comment section of the original defaming post. Some platforms allow you to leave comments, some don’t. A few even let you message a poster directly. In these instances, try baiting the hook with an “apology” or another type of luring message.
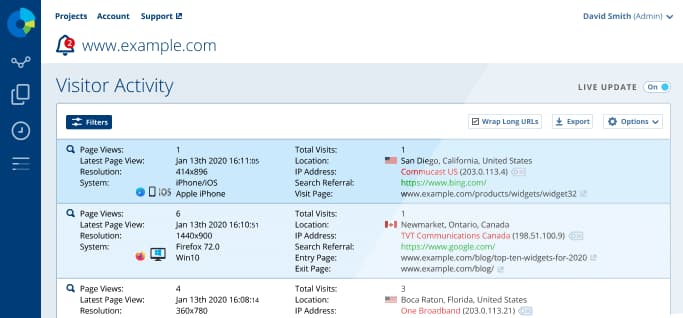
It isn’t too hard to set up your honeytrap blog. Reputation X has had success doing this sort of thing for clients. It simply requires setting up a blog using a hosting service like GoDaddy, WordPress, SquareSpace, etc. By placing IP address tracking software like StatCounter on your site, you can get the information you need from those that visit.
The key to a honeytrap website is to place a Noindex tag on the site so search engines will not crawl it. That way the site will not be visited by many, if any, people. The only person who visits the site will be your target.
Since your target’s identity is the only one you want, the goal is to get the honeytrap link in front of them only so you don’t have other people visiting your site and clouding your search. That’s why you only want to send the link to the email address you verified is connected to the person who made the defamatory comments. Similarly, you only want to message/reply to them on social networking platforms and message boards that you know are linked to that verified email address.
So you’ve got an IP address. Now what?
As previously mentioned, an IP address won’t give you your target’s exact location, but it will often get you close. To be fair, sometimes the IP is useless because companies that track IP locations don’t always know where the user is and will use the exact center of a country instead, as in the case of some unfortunate people who live in the precise center of the United States.
One way you possibly might be able to end the search quickly is if the source of the defaming comments is in your own company. To suss this out, you could try these methods during office hours. If your defamer is an internal source that likes to check personal emails during work, you can catch them in the act.
If you obtain an IP address and it’s one your company’s server uses, you’ve narrowed down your search to just your office, which might be all you need to close the case. Your company would have legal rights to obtain more information from an internal IP address than you would if you simply used one of the aforementioned IP address tracking tools.
What can you do if an IP address is not available?
An investigation into who is defaming you online is much easier if an IP address is available. However, sometimes a device’s IP address is hidden behind a personal ISP or by the user using a proxy or TOR.
In these cases, you’ll have to get creative and find a way to get your defamer to post or send you a document (such as a .pdf, .doc, .xls, .pps, or .ppt). These file types contain hidden metadata that can help in locating or identifying your target.
Few deserve to have their hard-earned personal brand or corporate reputation dragged through the mud. If someone does defame you online, know that there are steps you can take to find out who they are.
FAQs about identifying who is defaming you online
Who might be creating negative content about you online?
Places to look for defaming comments about you, your company, etc… include:
- Online message board (i.e., Yahoo Finance Board)
- New URLs (YourCompanySucks.com, for example)
- Emails to employees, clients, and competitors
- Wikipedia articles
What is an IP address?
An IP address is a unique identifier for an electronic communication device that uses the internet or a local network. IP stands for Internet Protocol which is the set of rules governing the data that is sent from these devices.
What is a device fingerprint?
A device fingerprint is a way to identify a device or browser by collecting unique information about its configuration. Using specific data points about their device you can create a view of the person defaming you.
Examples of device fingerprint data points include:
- IP address
- Browser plugins installed
- Time zone
- Installed fonts
- Timestamp
- Flash data from Flash plugin
- HTTP request headers
- Silverlight data
- User-agent string
- Mime-types
About the author
Kent Campbell is the chief strategist for Reputation X, an award-winning reputation management agency based in California. Kent has over 15 years of experience with SEO reputation management, Wikipedia editing, review management, and strategy. Kent has helped celebrities, leaders, executives, and marketing professionals improve the way they are seen online. Kent writes about reputation, SEO, Wikipedia, and PR-related topics, and is an expert witness for reputation-related legal matters. You can find Kent’s biography here.
–
Tags: Online Reputation Repair, Reputation Marketing, Reputation Protection.